Intro

Note: Kusama Shield has not been audited.
License:
Kusama Shield is developed under the MIT license.
Recommended wallet:
All current features have been tested with Talisman
Code repositories:
https://codeberg.org/KusamaShield/
- ZKSOLgen
ZK solidity verifier generator. - Interface
Kusama Shield React interface. - Solidity helpers
Solidity contracts and EVM helper scripts. - no-std Halo2 for Polkavm
Test instance:
https://kusamashield.laissez-faire.trade
How does Kusama Shield work?
Kusama Shield is a Zero Knowledge powerd multi-asset shielded pool, allowing anyone to deposit any supported token into the shielded pool and withdraw without a link inbetween, providing unlinkable transactions.
The project is being run as several autonomuos EVM compatible smart contracts on Kusama Assethub, powered by Risc-v PVM.
Smart contract architecture:
Kusama Shield consists of 4 main contracts that interact with eachother. For a more detailed view read the Zero Knowledge Circuit section here on the documentation page.
View source:
https://codeberg.org/KusamaShield/Solidity_helpers
How anonymous is the system?
Kusama Shield provides unlinkable transactions, a more detailed guide on how this works can be found in the ZK Ciruit section.
The privacy score can be measured by the K-anonymity score. Which roughly translates to the more users that deposit and withdraws at the same time, the higher anonymity the systems gets, the goal is to get lost in the crowd.
How does it compare to Monero?
Monero relies on decoy transactions. To calculate the anonymity score of your Monero transaction we need to look at a block explorer, and calculate
\( k = \frac{\text{Total number of decoys in the block}}{\text{Total number of transactions in the block}} \)
Supported assets
Kusama Shield supports all ethereum erc20 asset as well as the native token on the chain where it is deployed.
Supported Networks
- Westend Assethub | Testnet
- Moonbase | Testnet
- Paseo Contracts Chain | Testnet
- Kusama Assethub | Mainnet
For the latest features and most stable version use the paseo TESTNET version.
Moonbase and Westend is not actively maintained and should not be used.
Kusama Shield is compatible with any EVM chain that supports smart contracts in solidity and have an Ethereum RPC.
Westend Assethub
Note: Westend Assethub is currently bricked, use the Paseo chain instead
Faucet:
https://faucet.polkadot.io/westend?parachain=1000
Block explorer:
https://blockscout-asset-hub.parity-chains-scw.parity.io
Moonbase Testnet
Deployed contract address:
- Todo
Deployed contract source code:
- Todo
Faucet:
Block explorer:
Chain id:
1287
Project documentation page:
Reproduce ZK solidity code:
git clone https://codeberg.org/KusamaShield/ZKSOLgen
cd ZKSOLgen/ && cargo run
Shield assets with Kusama Shield on Moonbase:
- Coming soon
Paseo Assethub Testnet
Paseo Assethub aka the Polkadot Testnet. A stable testnet for Kusama and Polkadot.
Configure Metamask:

Get testnet tokens via Faucet:
Deployed contract address:
Deployed contract source code:
codeberg.org/KusamaShield/Solidity_helpers/contracts/paseo
Block explorers:
Ethereum RPC:
- https://eth-rpc-testnet.polkadot.io/
- https://services.polkadothub-rpc.com/testnet/
Native Asset:
PAS
Chain id:
420420417
Kusama Shield Paseo demo:
Read more about Paseo here:
Paseo.site
https://docs.polkadot.com/parachains/launch-a-parachain/deploy-to-polkadot/#get-started-with-an-account-and-tokens
https://github.com/paseo-network
Kusama Assethub Mainnet
Deployed contracts:
- [ZK Verifier] 0xc81D878518791fE261841a1eF7Eb7cc565598Ae4
- [Poseidon Hasher] 0x02bB94D5eeEAc7C102D90e661BB925d0BE98E639
- [Shielded Pool] 0xDC80565357D63eCa67F3f020b6DD1CE1fD0E1Ed8
Kusama Assethub EVM RPC's:
- https://kusama-rpc.laissez-faire.trade
- https://kusama-asset-hub-eth-rpc.polkadot.io
- https://eth-asset-hub-kusama.dotters.network
How to fund an EVM account on Kusama Assethub.
XCM tokens from Kusama to Kusama Assethub:
app.turtle.cool is an easy to use tool to send your KSM from Kusama to Kusama Assethub.
Account conversion:
When we make transactions we are doing this from an ethereum account in an ethereum way, in order to do so we must send funds from our regular substrate address to the EVM address we want to use.
Let's create a new ethereum account and send funds to it:
cast wallet new
Successfully created new keypair.
Address: 0xbe386C4368Fadf622830d00e2353D4dF5fEE52Ac
Private key: 0x45f3cb7cd86153b09b83c914c9306161e790738295a209334f35127d45897639
Take the Address and append 24 small e:
0xbe386C4368Fadf622830d00e2353D4dF5fEE52Aceeeeeeeeeeeeeeeeeeeeeeee
send a balance transfer to this account like this:
https://assethub-kusama.subscan.io/extrinsic/10684721-2
How to use Kusama Shield on Kusama Assethub:
Note: make sure you have balance on your ETHEREUM account on Kusama Assethub
1: Connect wallet:

2: Select Amount

3: Save token
Next you will have a secret token being generated for you, when you want to withdraw you neeed to know the amount and this secret token.
Redeploying the shielded pool:
- 1: Deploy the PolkaVM poseidon project
- 2: deploy the zk verifier
- 3: Link the poseidon contract into InternalLeanIMT
- 4: Link the zk contract address into the FixedIlop/Shielded Pool contract
- 5: Deploy the Shielded pool with the script provided in same repo
- 6: Test withdrawals and deposits with this script:
https://codeberg.org/KusamaShield/Solidity_helpers/src/branch/main/contracts/paseo2_kusama/test_deposit_withdraw.js
Zero Knowledge Circuits
The ZK logic is using a LeanIMT merkle tree, as its one of the few audited merkle tree's recommended by ZK-kit.
All circuits are written in Circom, if you are new to circom, we recommend you go throw this tutorials:
https://learn.0xparc.org/materials/circom/learning-group-1/intro-zkp/
Source code:
https://codeberg.org/KusamaShield/Solidity_helpers/src/branch/main/contracts/new_circuits
Circuits explaination
A ZK-SNARK circuit system built with Circom 2.1 and Groth16 on BN254. It enables private withdrawals from an on-chain commitment pool with UTXO-style commitment refresh for transaction unlinkability.
Overview
A user deposits funds by publishing a commitment (a Poseidon hash encoding value, asset type, nullifier, and secret) into an on-chain Merkle tree. To withdraw, the user generates a zero-knowledge proof that they know the preimage of some commitment in the tree — without revealing which one. The spent commitment is invalidated via a nullifier hash, and a new "change" commitment is inserted back into the tree.
Circuit Architecture
withdraw.circom ← top-level circuit (orchestrator)
├── commitment.circom ← three-layer Poseidon commitment scheme
│ └── poseidon_bn254.circom ← Poseidon hash wrapper (BN254)
└── merkle_tree.circom ← LeanIMT variable-depth inclusion proof
└── poseidon_bn254.circom
poseidon_bn254.circom — Hash Primitive
A parameterized wrapper around circomlib's Poseidon hash. Poseidon is a ZK-friendly hash function — far cheaper inside an arithmetic circuit than SHA-256 or Keccak.
PoseidonBN254(n): signal input in[n] → signal output out
commitment.circom — Three-Layer Commitment
Constructs a commitment in three layers, each serving a distinct purpose:
| Layer | Computation | Purpose |
|---|---|---|
| 1 | nullifierHash = Poseidon(nullifier) | Published on-chain to prevent double-spending |
| 2 | precommitment = Poseidon(nullifier, secret) | Binds the nullifier to a secret only the owner knows |
| 3 | commitment = Poseidon(value, asset, precommitment) | The Merkle tree leaf, encoding value and asset type |
Separating the nullifier hash from the secret allows the nullifier to be revealed (marking a commitment as spent) without leaking the secret or the commitment's position in the tree.
merkle_tree.circom — LeanIMT Inclusion Proof
Implements a Lean Incremental Merkle Tree inclusion proof with variable depth (up to maxDepth = 254).
At each tree level:
- The
leafIndexbits determine left/right child ordering. - If a sibling is zero (empty subtree), the node propagates unchanged — this is the "lean" optimization that avoids hashing against placeholder nodes.
- If a sibling is non-zero, the ordered pair is hashed with Poseidon.
The computed root is compared against the public root input. This approach is more constraint-efficient than a fixed-depth tree because most levels in a sparse tree have zero siblings.
withdraw.circom — Main Circuit
The top-level Withdraw(254) template orchestrates the full proof in eight steps:
| Step | Operation | Description |
|---|---|---|
| 1 | Compute existing commitment | Hashes (existingValue, asset, existingNullifier, existingSecret) through the three-layer scheme |
| 2 | Output nullifier hash | Published on-chain so the contract can reject double-spends |
| 3 | Merkle inclusion proof | Verifies the existing commitment is in the tree against the public root |
| 4 | 128-bit range checks | Constrains both withdrawnValue and remainingValue to 128 bits (prevents underflow/overflow) |
| 5 | Nullifier uniqueness | Asserts existingNullifier != newNullifier to prevent nullifier reuse |
| 6 | Compute new commitment | Hashes (remainingValue, asset, newNullifier, newSecret) — the "change" UTXO |
| 7 | Output new commitment | Inserted into the on-chain tree by the contract |
| 8 | Replay protection | Constrains context into the proof (e.g., chain ID or tx hash) to prevent cross-chain/cross-tx replay |
Signals
Public inputs:
withdrawnValue— amount being withdrawnroot— current Merkle tree roottreeDepth— actual depth of the treecontext— replay protection binding (chain ID, tx hash, etc.)
Public outputs:
existingNullifierHash— marks the old commitment as spentnewCommitmentHash— the change commitment to insert into the tree
Private inputs:
asset— asset identifierexistingValue,existingNullifier,existingSecret— preimage of the spent commitmentnewNullifier,newSecret— fresh randomness for the change commitmentsiblings[254],leafIndex— Merkle proof path
Privacy Properties
- Sender privacy — the Merkle path is private, so the proof doesn't reveal which commitment is being spent.
- Transaction unlinkability — each withdrawal creates a fresh commitment with a new nullifier and secret, preventing linkage of sequential transactions by the same user.
- Double-spend prevention — the nullifier hash is published on-chain; the contract rejects any previously-seen nullifier hash.
- Value integrity — 128-bit range checks ensure no one can create value from nothing or withdraw more than they deposited.
- Replay protection — the
contextbinding prevents proof reuse across different chains or transactions.
Supported Wallets
Kusama Shield mainly supports EVM based browser wallets. Most features are tested with Talisman or Metamask wallet.
Polkadot / Substrate Wallets
Connected via @talismn/connect-wallets and @polkadot/extension-dapp.
| Wallet | Description |
|---|---|
| Polkadot.js | Official Polkadot browser extension |
| Talisman | Multi-chain wallet for Polkadot & Ethereum |
| SubWallet | Comprehensive Polkadot ecosystem wallet |
| Nova Wallet | Mobile-first Polkadot wallet |
| Fearless Wallet | DeFi wallet for the Polkadot ecosystem |
| PolkaGate | Polkadot browser extension wallet |
| Enkrypt | Multi-chain browser extension by MyEtherWallet |
| Manta Wallet | Privacy-focused wallet for Manta Network |
| Aleph Zero Wallet | Wallet for the Aleph Zero network |
EVM Wallets
| Wallet | Description |
|---|---|
| MetaMask | Most widely used Ethereum browser extension |
| Coinbase Wallet | Coinbase self-custody wallet |
| Trust Wallet | Multi-chain mobile wallet |
| Rainbow | Ethereum wallet with NFT support |
| Rabby | Rabby wallet |
| Zerion | DeFi-focused wallet |
| WalletConnect | QR-code-based protocol connecting 300+ mobile wallets |
Any wallet that supports the WalletConnect protocol can connect to this application. This is over 200 different EVM wallets.
Poseidon on PolkaVM
Poseidon is a cryptographic hash function designed specifically for zero-knowledge proof systems (like zk-SNARKs and zk-STARKs), where it needs to be efficient to compute inside arithmetic circuits. It works by processing input data through multiple rounds of substitution-permutation network (SPN) operations over a finite field, using only addition, multiplication, and power functions with small exponents (typically $x^5$ or $x^3$).
Unlike traditional hash functions (SHA-256, Blake2) that use bitwise operations and modular arithmetic—operations expensive to represent in circuits—Poseidon's arithmetic-friendly design minimizes the number of constraints needed in zk-proofs.
Core Structure
The hash consists of three main operations:
- AddRoundConstants — adding fixed field elements
- S-Boxes — applying the power function to a subset of state elements
- MixLayer — multiplying the state by an MDS matrix for diffusion
By carefully balancing full rounds (S-Boxes applied to all elements) with partial rounds (S-Boxes applied to just one element), Poseidon achieves both security and circuit efficiency, making it the go-to choice for hashing in modern blockchain scaling solutions and privacy protocols.
Poseidon White paper - POSEIDON: A New Hash Function for Zero-Knowledge Proof Systems
The solidity implementation was not working for PolkaVM and Kusama Assethub so we decided to port it to PolkaVM.
Repo:
https://codeberg.org/KusamaShield/PoseidonPolkaVM
Call the poseidon hasher on-chain:
cast call 0x1d165f6fE5A30422E0E2140e91C8A9B800380637 "hash(uint256[2]):(uint256)" "[123,456]" --rpc-url https://eth-rpc-testnet.polkadot.io
19620391833206800292073497099357851348339828238212863168390691880932172496143
Use:
Kusama Shield utilize Poseidon in it's on-chain merkle tree.
Compatibility:
PoseidonPolkaVM is compatible with:
- Circom
https://github.com/iden3/circomlib/blob/master/circuits/poseidon.circom - Light-Poseidon
https://www.npmjs.com/package/poseidon-lite - Solidity
Example usecase:
https://codeberg.org/KusamaShield/Solidity_helpers/src/branch/main/contracts/paseo/InternalLeanIMT.sol
Making it easy to integrate into your smart contract zk logic on Kusama Assethub.
How Poseidon Works in PoseidonPolkaVM
This document explains the Poseidon hash function as implemented in this repository — a PolkaVM-compatible, Solidity-friendly port built on the BN254 scalar field with Montgomery arithmetic.
Table of Contents
- Overview
- The BN254 Finite Field
- Montgomery Form Arithmetic
- The Poseidon Permutation
- Parameters
- Solidity / PolkaVM Interface
- Lean Indexed Merkle Tree
- Test Vectors
Overview
Poseidon is a cryptographic hash function designed specifically for zero-knowledge proof systems. Unlike general-purpose hash functions (SHA-256, Keccak), Poseidon operates natively over prime fields, making it extremely efficient inside arithmetic circuits (SNARKs, STARKs).
This implementation:
- Targets the BN254 scalar field (the same field used by Ethereum's
ecPairingprecompile and Circom/Groth16). - Uses arity 2: it takes two field elements as input and produces one field element as output.
- Is fully compatible with CircomZK / Solidity Poseidon libraries (same constants, same outputs).
- Runs on PolkaVM (Polkadot's RISC-V based virtual machine) as a smart contract.
Reference: Poseidon: A New Hash Function for Zero-Knowledge Proof Systems (2019)
The BN254 Finite Field
All arithmetic happens in the scalar field of the BN254 (alt_bn128) elliptic curve. This is the field of integers modulo the prime:
p = 21888242871839275222246405745257275088548364400416034343698204186575808495617
In hex:
p = 0x30644e72e131a029b85045b68181585d2833e84879b9709143e1f593f0000001
A field element is represented as four 64-bit limbs (little-endian):
#![allow(unused)] fn main() { #[derive(Clone, Copy, PartialEq, Eq)] pub struct Fr([u64; 4]); // 256-bit field element }
All operations (addition, multiplication) produce results in the range [0, p-1].
Montgomery Form Arithmetic
Direct modular arithmetic requires expensive division for every reduction step. This implementation avoids that by using Montgomery form, where every field element a is stored as:
a_mont = a * R mod p where R = 2^256
Why Montgomery Form?
The key insight is that Montgomery multiplication computes:
MontMul(a_mont, b_mont) = a_mont * b_mont * R^(-1) mod p
= (a * R) * (b * R) * R^(-1) mod p
= a * b * R mod p
= (a * b)_mont
This replaces modular division with shifts and additions, which is much faster.
Key Constants
| Constant | Value | Purpose |
|---|---|---|
MODULUS | The prime p as 4 limbs | Field modulus |
INV | -p^(-1) mod 2^64 | Montgomery reduction factor |
R2 | R^2 mod p | Used to convert normal -> Montgomery form |
R_MOD_P | R mod p | Montgomery representation of 1 |
Conversion
- Normal to Montgomery:
a_mont = MontMul(a, R^2) = a * R^2 * R^(-1) = a * R mod p - Montgomery to Normal:
a = MontMul(a_mont, 1) = a_mont * 1 * R^(-1) = a * R * R^(-1) = a mod p
CIOS Multiplication Algorithm
The implementation uses the Coarsely Integrated Operand Scanning (CIOS) variant of Montgomery multiplication (src/zk.rs). For each limb i of the multiplier:
- Multiply-accumulate: Compute partial products
a[j] * b[i]and accumulate into a temporary buffert[0..5]. - Reduce: Compute
m = t[0] * INV mod 2^64, then addm * MODULUSto cancel out the lowest limb. - Shift: Move the result down by one limb position.
- Final subtraction: If the result exceeds
p, subtractponce.
Addition
Field addition computes a + b mod p using 128-bit additions with carry propagation, followed by a conditional subtraction of p if the result overflows.
The Poseidon Permutation
The Poseidon hash applies a sponge construction with a specialized permutation. Here is the complete flow:
State Initialization
The state is a vector of T = 3 field elements (state width = arity + 1):
state = [0, input[0], input[1]]
The first element (index 0) is the capacity element, initialized to zero. The remaining elements hold the inputs.
The Round Function
Each of the 65 rounds applies three layers in sequence:
┌──────────────────────────────────────────────────────────────────────┐
│ For each round r = 0..64: │
│ │
│ 1. ARK: state[i] += ROUND_CONSTANTS[r * 3 + i] for i in 0..3 │
│ 2. SBOX: state[i] = state[i]^5 (full or partial)│
│ 3. MDS: state = MDS_MATRIX * state │
│ │
└──────────────────────────────────────────────────────────────────────┘
Add Round Constants (ARK)
Each round adds a unique set of constants to the state. There are 195 round constants total (65 rounds x 3 state elements). These constants are generated deterministically using the Grain LFSR as specified in the Poseidon paper:
sage generate_parameters_grain.sage 1 0 254 3 8 57 <field_prime>
The constants are pre-computed and stored in Montgomery form in ROUND_CONSTANTS.
S-box Layer
The S-box is the non-linear component that provides cryptographic security. It computes x^5 (alpha = 5):
#![allow(unused)] fn main() { fn sbox(x: &Fr) -> Fr { let x2 = x.mul(x); // x^2 (1 multiplication) let x4 = x2.mul(&x2); // x^4 (1 multiplication) x4.mul(x) // x^5 (1 multiplication) } }
This is computed in 3 multiplications using the addition chain: 1 -> 2 -> 4 -> 5.
MDS Matrix Multiplication
The Maximum Distance Separable (MDS) matrix provides diffusion — it ensures that every input bit affects every output bit. The 3x3 MDS matrix multiplication is:
new_state[0] = MDS[0][0]*state[0] + MDS[0][1]*state[1] + MDS[0][2]*state[2]
new_state[1] = MDS[1][0]*state[0] + MDS[1][1]*state[1] + MDS[1][2]*state[2]
new_state[2] = MDS[2][0]*state[0] + MDS[2][1]*state[1] + MDS[2][2]*state[2]
The MDS matrix is a fixed, pre-computed constant derived from a Cauchy matrix, stored in Montgomery form. It is the same matrix used by the circomlib Poseidon implementation, ensuring output compatibility.
Full Rounds vs Partial Rounds
This is the key optimization of Poseidon over earlier designs:
Round 0 ─┐
Round 1 │ Full Rounds (first half: 4 rounds)
Round 2 │ → S-box applied to ALL 3 state elements
Round 3 ─┘
Round 4 ─┐
... │ Partial Rounds (57 rounds)
... │ → S-box applied ONLY to state[0]
Round 60 ─┘
Round 61 ─┐
Round 62 │ Full Rounds (second half: 4 rounds)
Round 63 │ → S-box applied to ALL 3 state elements
Round 64 ─┘
- Full rounds (8 total, split 4+4): Apply x^5 to every state element. This provides wide diffusion at the start and end.
- Partial rounds (57 total): Apply x^5 only to
state[0]. The MDS matrix still spreads the non-linearity to all elements.
This "sandwich" structure (full-partial-full) dramatically reduces the number of multiplications while maintaining the same security level. In arithmetic circuits (ZK proofs), this translates to far fewer constraints.
Output
After all 65 rounds, the hash output is state[0] — the capacity element:
#![allow(unused)] fn main() { pub fn poseidon(inputs: &[Fr; 2]) -> Fr { // ... 65 rounds of ARK + SBOX + MDS ... state[0] // Return first element } }
Parameters
| Parameter | Value | Description |
|---|---|---|
| Field | BN254 scalar field | 254-bit prime field |
| Arity | 2 | Number of inputs |
| State width (T) | 3 | Capacity (1) + Arity (2) |
| Alpha (S-box) | 5 | Exponent for S-box: x^5 |
| Full rounds | 8 | Split as 4 + 4 |
| Partial rounds | 57 | S-box only on state[0] |
| Total rounds | 65 | 8 + 57 |
| Round constants | 195 | 65 rounds x 3 elements |
| MDS matrix | 3x3 | Fixed Cauchy-derived matrix |
Solidity / PolkaVM Interface
The hash function is exposed as a PolkaVM smart contract with a Solidity-compatible ABI:
function hash(uint256[2] memory input) external pure returns (uint256);
Function selector: 0x561558fe
Call Flow
Solidity caller
│
▼
ABI-encoded calldata (68 bytes)
[4-byte selector][32-byte uint256][32-byte uint256]
│
▼
Decode via ethabi
│
▼
Convert big-endian bytes → little-endian u64 limbs → Fr (Montgomery form)
│
▼
poseidon(&[fr_a, fr_b])
│
▼
Convert Fr → limbs → big-endian bytes (32 bytes)
│
▼
Return via PolkaVM UAPI
Byte Order Conversion
Ethereum uses big-endian 256-bit integers. The Fr type uses little-endian 64-bit limbs. The conversion reverses the limb order and byte order:
Ethereum: [byte_0, byte_1, ..., byte_31] (big-endian)
────────────────────────────────
Fr limbs: [limb_0, limb_1, limb_2, limb_3] (little-endian)
where limb_0 = least significant 64 bits
Lean Indexed Merkle Tree
The repository also includes a generic Lean Indexed Merkle Tree (src/leanimt.rs) that can use Poseidon as its hash function. This is a binary Merkle tree where:
- Leaves are hashed pairwise up to a single root.
- New leaves can be inserted incrementally without rebuilding the entire tree.
- The tree depth grows as needed.
This is useful for building commitment schemes and membership proofs in ZK applications.
Test Vectors
These test vectors are verified against the reference CircomZK/Solidity Poseidon implementations:
| Input | Output |
|---|---|
[0, 0] | 5520371747610818048552497760483731695918538905235353263918705622436011791040 |
[1, 2] | 3240460917331939313458239639914504962640333851982787431747809795119847651274 |
[123, 456] | 10422317022970317265083564129867363010880980031113186224756990573079674352133 |
Cross chain Swaps
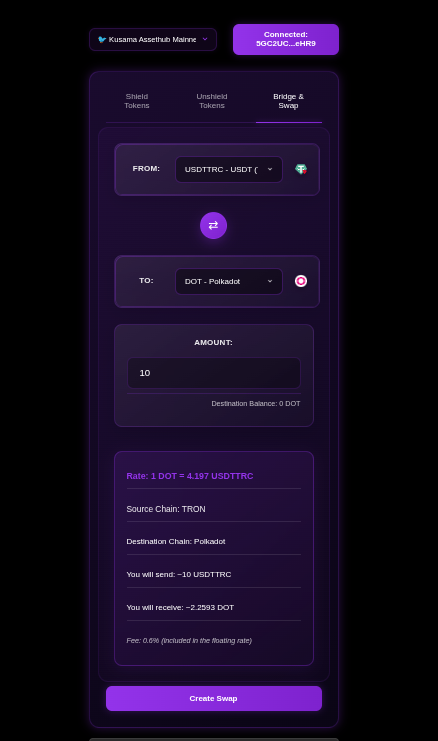
Note: Not all pairs and tokens have been fully tested, we have mostly tested the USDT trx to DOT transfers.
The long term vision of Kusama Shield is to build up the world's biggest anonymity set. A home for your shielded Asset's. By tapping into to various DEFI protocols we are able to facilitate easy to use swaps. Allowing third party ecosystem to easily swap their crypto currency into DOT and then KSM to be able to hold shielded KSM.
Dot > KSM
See next page for further information.
Crypto Currency > DOT on Assethub
Tap into third party liquidity and swap your tokens into DOT for a low fee.
Avaliable swaps are:
| Asset | Destination |
|---|---|
| AAVEETH | Polkadot Assethub |
| ADA | Polkadot Assethub |
| APT | Polkadot Assethub |
| ARB | Polkadot Assethub |
| ATOM | Polkadot Assethub |
| AVAX | Polkadot Assethub |
| BAT | Polkadot Assethub |
| BCH | Polkadot Assethub |
| BNBOPBNB | Polkadot Assethub |
| BSC | Polkadot Assethub |
| BTC | Polkadot Assethub |
| BTCBSC | Polkadot Assethub |
| BTCLN | Polkadot Assethub |
| BTT | Polkadot Assethub |
| CAKE | Polkadot Assethub |
| DAIBSC | Polkadot Assethub |
| DAIETH | Polkadot Assethub |
| DASH | Polkadot Assethub |
| DOGE | Polkadot Assethub |
| ETC | Polkadot Assethub |
| ETH | Polkadot Assethub |
| ETHARBITRUM | Polkadot Assethub |
| ETHBASE | Polkadot Assethub |
| ETHBSC | Polkadot Assethub |
| ETHOP | Polkadot Assethub |
| KCS | Polkadot Assethub |
| LINK | Polkadot Assethub |
| LTC | Polkadot Assethub |
| MANAETH | Polkadot Assethub |
| PAXGETH | Polkadot Assethub |
| PEPEETH | Polkadot Assethub |
| POL | Polkadot Assethub |
| POL | Polkadot Assethub |
| POLETH | Polkadot Assethub |
| S | Polkadot Assethub |
| SHIB | Polkadot Assethub |
| SOL | Polkadot Assethub |
| SUI | Polkadot Assethub |
| TON | Polkadot Assethub |
| TRX | Polkadot Assethub |
| TUSD | Polkadot Assethub |
| TWTBSC | Polkadot Assethub |
| USDCARBITRUM | Polkadot Assethub |
| USDCBSC | Polkadot Assethub |
| USDCETH | Polkadot Assethub |
| USDCSOL | Polkadot Assethub |
| USDP | Polkadot Assethub |
| USDT | Polkadot Assethub |
| USDTARBITRUM | Polkadot Assethub |
| USDTBSC | Polkadot Assethub |
| USDTMATIC | Polkadot Assethub |
| USDTSOL | Polkadot Assethub |
| USDTTRC | Polkadot Assethub |
| WBNBBSC | Polkadot Assethub |
| WETHARBITRUM | Polkadot Assethub |
| WETHETH | Polkadot Assethub |
| WSOL | Polkadot Assethub |
| XLM | Polkadot Assethub |
| XTZ | Polkadot Assethub |
| ZEC | Polkadot Assethub |
| ZRX | Polkadot Assethub |
Example, Zec > DOT:
Send ZEC to DOT on assethu demo:
https://x.com/KusamaShield/status/1991508308260450656?t=2jdGeL-q_PnlqRa6lRissg&s=19
DOT > KSM
Send DOT from Polkadot Assethub chain to Kusama Assethub using Polkadot Assethub's DEX and then send KSM to Kusama Assethub.
Technical overview:
- 1: Swap DOT to KSM using Polkadot Assethub's on-chain DEX
- 2: Send the KSM to Kusama Assethub using Snowbridge's trustless bridge
Demo:
DOT Polkadot assethub to Kusama Assethub KSM
How to:
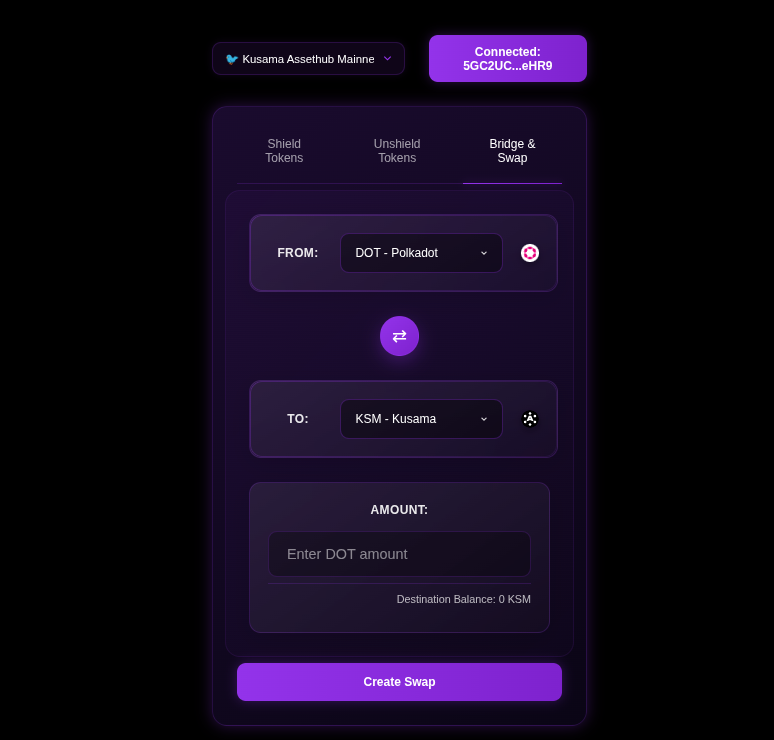
Step 1:
Connect your Talisman browser wallet and select your polkadot account. Make sure you have funds on Polkadot Assethub not regular Polkadot Relay chain.
Step 2:
Navigate to bridge tab and select the amount of DOT you want to swap. You will be able to preview the rate before the swap takes place.
Step 3:
Press swap and approve the transactions, Because Kusama Shield tries to be EVM compatible we ask the user to first select their Polkadot wallet then switch to the connected address to your talisman Ethereum account. This makes it much easier to be able to directly shield your KSM, once you have swapped them.
Step 4:
Shield your fresh KSM.
Other interfaces:
https://kheopswap.xyz/#/polkadot/swap
Snowbridge trustless bridge documentation
Cross-Chain Swap Guide
Kusama Shield provides low cost cross-chain swaps, allowing users to exchange DOT for a wide variety of digital assets across different blockchain networks. And send the DOT to Kusama Assethub to provide shielded KSM and more privacy.
Note: Kusama Shield has not been audited, proceed with care. Application assumes that you have connected a Talisman browser wallet.
Overview
The swap functionality enables you to:
- Convert DOT to/from 50+ different cryptocurrencies(on other l1 and l2 chains)
- Swap between major blockchains (Bitcoin, Ethereum, Solana, etc.)
- Track your swap status in real-time
- By utilizing the dotsend bot we are able to provide fast and lowcost(0.6% fee) swaps.
Demo:
Send USDT(trc20) from Tron, that the user has in Trust wallet to DOT.
How to Use Swaps
Note: Tested with chrome browser + Talisman wallet
1. Connect Your Wallet
- Click "Connect Wallet" in the interface
- Select your preferred Polkadot wallet (Talisman, Polkadot.js, SubWallet)
- Ensure your wallet contains DOT tokens
2. Navigate to Bridge & Swap
- Select the "Bridge & Swap" tab in the main interface
- This feature is available on Kusama AssetHub mainnet
3. Configure Your Swap
From Currency
- DOT is currently the primary source currency
- Enter the amount of DOT you want to swap
To Currency
Choose from 80+ available destination currencies including:
- Bitcoin Network: BTC, BTCLN (Lightning), BTCBSC
- Ethereum Network: ETH, ETHOP, ETHARBITRUM, ETHZKSYNC
- Stablecoins: USDT, USDTBSC, USDTMATIC, USDC, DAI
- Major Altcoins: ADA, SOL, AVAX, ATOM, APT, LINK
- DeFi Tokens: AAVE, UNI, CAKE, SUSHI
- And many more
Destination Address
- For DOT → KSM swaps: Uses your connected wallet address automatically
- For other destinations: Enter the destination address for the target network
- Important: Ensure the address format matches the destination blockchain
4. Review Exchange Rate
- The interface displays the current exchange rate
- Shows estimated amount you'll receive
- Rates are fetched in real-time from the swap provider
5. Create Swap:
- Click "Create Swap" to initiate the process
- A QR code will be generated for the deposit address
- Copy the deposit address or scan the QR code with your wallet
6. Send Your DOT:
- Send the exact DOT amount to the provided deposit address
- Click "I've sent the DOT" once the transaction is broadcast
- Do not send more or less than the specified amount
7. Track Your Swap
The interface provides real-time status updates:
Status Stages
- NEW: Order created, waiting for your deposit
- PENDING: Deposit received, confirming on blockchain
- EXCHANGE: Funds confirmed, exchange in progress
- WITHDRAW: Sending tokens to your destination address
- DONE: Swap completed successfully
Transaction Details
- Deposit Transaction: Hash, amount, fees, confirmations
- Withdrawal Transaction: Hash, amount, fees, confirmations
- Destination Address: Where your tokens are being sent
- Time Tracking: Order creation, processing times, completion
8. Completion
- Receive confirmation when swap is complete
- Transaction hashes are provided for verification
- Tokens are sent to your specified destination address
Available Trading Pairs:
DOT to Other Cryptocurrencies (50+ pairs)
Bitcoin Networks:
- DOT → BTC (Bitcoin)
- DOT → BTCLN (Bitcoin Lightning)
- DOT → BTCBSC (Bitcoin on BSC)
- DOT → BCH (Bitcoin Cash)
Ethereum Ecosystem:
- DOT → ETH (Ethereum)
- DOT → ETHOP (Ethereum Optimism)
- DOT → ETHARBITRUM (Ethereum Arbitrum)
- DOT → ETHZKSYNC (Ethereum zkSync)
- DOT → ETHBASE (Ethereum Base)
Stablecoins:
- DOT → USDT (Tether)
- DOT → USDTBSC (Tether BSC)
- DOT → USDTMATIC (Tether Polygon)
- DOT → USDTARBITRUM (Tether Arbitrum)
- DOT → USDTSOL (Tether Solana)
- DOT → USDTTRC (Tether TRON)
- DOT → USDC (USD Coin)
- DOT → USDCBSC (USD Coin BSC)
- DOT → USDCARBITRUM (USD Coin Arbitrum)
- DOT → USDCSOL (USD Coin Solana)
- DOT → DAI (Dai)
- DOT → DAIBSC (Dai BSC)
- DOT → DAIMATIC (Dai Polygon)
- DOT → TUSD (TrueUSD)
- DOT → USDP (Pax Dollar)
Major Blockchains:
- DOT → KSM (Kusama) Special cross-chain route
- DOT → ADA (Cardano)
- DOT → SOL (Solana)
- DOT → AVAX (Avalanche)
- DOT → ATOM (Cosmos)
- DOT → APT (Aptos)
- DOT → SUI (Sui)
- DOT → TON (Toncoin)
- DOT → XRP (Ripple)
- DOT → LTC (Litecoin)
- DOT → DOGE (Dogecoin)
DeFi & Exchange Tokens:
- DOT → AAVE (Aave)
- DOT → LINK (Chainlink)
- DOT → UNI (Uniswap)
- DOT → CAKE (PancakeSwap)
- DOT → SHIB (Shiba Inu)
Privacy Coins:
- DOT → XMR (Monero)
- DOT → ZEC (Zcash)
- DOT → DASH (Dash)
Other Networks:
- DOT → TRX (TRON)
- DOT → VET (VeChain)
- DOT → XLM (Stellar)
- DOT → XTZ (Tezos)
- DOT → ETC (Ethereum Classic)
Cryptocurrencies to DOT (50+ pairs)
You can swap the following cryptocurrencies to DOT:
Bitcoin Networks:
- BTC → DOT (Bitcoin)
- BTCLN → DOT (Bitcoin Lightning)
- BTCBSC → DOT (Bitcoin on BSC)
- BCH → DOT (Bitcoin Cash)
Ethereum Ecosystem:
- ETH → DOT (Ethereum)
- ETHARBITRUM → DOT (Ethereum Arbitrum)
- ETHBASE → DOT (Ethereum Base)
- ETHBSC → DOT (Ethereum on BSC)
- ETHOP → DOT (Ethereum Optimism)
- ETHZKSYNC → DOT (Ethereum zkSync)
- WETHETH → DOT (Wrapped ETH)
- WETHARBITRUM → DOT (Wrapped ETH Arbitrum)
- WETHBASE → DOT (Wrapped ETH Base)
Stablecoins:
- USDT → DOT (Tether)
- USDTBSC → DOT (Tether BSC)
- USDTMATIC → DOT (Tether Polygon)
- USDTARBITRUM → DOT (Tether Arbitrum)
- USDTSOL → DOT (Tether Solana)
- USDTTRC → DOT (Tether TRON)
- USDCETH → DOT (USD Coin Ethereum)
- USDCBSC → DOT (USD Coin BSC)
- USDCARBITRUM → DOT (USD Coin Arbitrum)
- USDCMATIC → DOT (USD Coin Polygon)
- USDCSOL → DOT (USD Coin Solana)
- DAIBSC → DOT (Dai BSC)
- DAIETH → DOT (Dai Ethereum)
- TUSD → DOT (TrueUSD)
- USDP → DOT (Pax Dollar)
Major Blockchains:
- ADA → DOT (Cardano)
- SOL → DOT (Solana)
- WSOL → DOT (Wrapped Solana)
- AVAX → DOT (Avalanche)
- ATOM → DOT (Cosmos)
- APT → DOT (Aptos)
- TON → DOT (Toncoin)
- XRP → DOT (Ripple)
- LTC → DOT (Litecoin)
- DOGE → DOT (Dogecoin)
DeFi & Exchange Tokens:
- AAVEETH → DOT (Aave Ethereum)
- LINK → DOT (Chainlink)
- CAKE → DOT (PancakeSwap)
- SHIB → DOT (Shiba Inu)
- PEPEETH → DOT (Pepe Ethereum)
- PAXGETH → DOT (PAX Gold Ethereum)
- MANAETH → DOT (MANA Ethereum)
- ZRX → DOT (0x Protocol)
- BAT → DOT (Basic Attention Token)
Privacy & Alternative Coins:
- XMR → DOT (Monero) Privacy coin
- ZEC → DOT (Zcash)
- DASH → DOT (Dash)
- ETC → DOT (Ethereum Classic)
- VET → DOT (VeChain)
- XLM → DOT (Stellar)
- XTZ → DOT (Tezos)
Other Networks & Tokens:
- TRX → DOT (TRON)
- BTT → DOT (BitTorrent Token)
- POL → DOT (Polygon)
- POLETH → DOT (Polygon Ethereum)
- KCS → DOT (KuCoin Token)
- BNBOPBNB → DOT (BNB Optimism)
- WBNBBSC → DOT (Wrapped BNB BSC)
- TWTBSC → DOT (Trust Wallet Token BSC)
- BSC → DOT (Binance Smart Chain)
- S → DOT (Specialty token)
Total: 70+ cryptocurrencies can be swapped to DOT
Special Features
DOT ↔ KSM Cross-Chain Swaps
- Direct integration with Polkadot and Kusama
- Uses on-chain DEX for optimal rates
- Automatic address handling for connected wallets
- No manual destination address required
See previous page for DOT > KSM swaps
Smart Status Tracking
- Adaptive Polling: Faster updates during critical phases
- Visual Progress: Step-by-step progress indicators
- Copy Functions: Easy copying of transaction hashes and addresses
- Emergency Handling: Clear instructions if manual review needed
Important Notes
Before Swapping
- ✅ Verify destination address format matches the target blockchain
- ✅ Check minimum and maximum swap amounts
- ✅ Ensure you have enough DOT for the swap amount
- ✅ Double-check the exchange rate and expected output
During Swaps
- ⏱️ Send the exact amount shown - not more, not less
- ⏱️ Don't send from exchange wallets (use personal wallets only)
- ⏱️ Keep the swap interface open to monitor progress
- ⏱️ Save transaction hashes for your records
- ⏱️ Keep in mind this is early(beta) software
After Completion
- 🔍 Verify receipt of tokens at destination address
- 🔍 Check transaction on destination blockchain explorer
- 🔍 Swap DOT to KSM and shield it for privacy
Troubleshooting
Emergency Status
If your swap enters "EMERGENCY" status:
- Don't panic - this requires manual review
- Email: kusamashield@smokes.thc.org
- Include: Your order number (displayed in the interface)
- Response: Support will resolve issues quickly
Common Issues
- Wrong Address Format: Ensure destination address matches target blockchain
- Insufficient Funds: Verify you have enough DOT for the swap
- Network Delays: Blockchain congestion can cause delays
- Expired Orders: Complete swaps within the time limit
Support
- Documentation: https://kusamashield.codeberg.page
- Emergency Support: kusamashield[replace me with the digital cyber post a]smokes.thc.org
- Status Page: Monitor service status on the main interface
Technical Details
Supported Networks
- Polkadot Ecosystem: DOT, KSM parachains
- Bitcoin: BTC, Lightning Network, wrapped variants
- Ethereum: Mainnet, L2s (Arbitrum, Optimism, Base, zkSync)
- Alternative L1s: Solana, Avalanche, Cosmos, Cardano
- Other Networks: BSC, Polygon, TRON, and more
Integration
- External Partners: Established swap providers for other pairs
- Real-time APIs: Live rate fetching and status tracking
- Blockchain Monitoring: Multi-chain transaction confirmation
For the latest updates and additional information, visit the official Kusama Shield documentation and follow us on X.
Swap USDT on Tron
Swapping USDT(trc20) on Tron from Trust wallet to DOT in my talisman browser wallet.
Demo:
Video demo sending from Trust wallet
Try it today:
UI Customization
Overview
The Kusama Shield UI supports visual customization to personalize the privacy experience.
Available Customizations
Rain Mode
Creates animated particle effects (rain/snow) across the screen. See Rain Mode Configuration for details.
Privacy Dashboard
View shielded balances, transaction history, and Merkle tree state. (Documentation coming soon)
Accessing Settings
- Click the toolbox icon in the main interface
- Settings modal opens with customization options
- Changes apply immediately to the preview
Rain Mode Configuration
Overview
Rain/Snow animation mode adds customizable particle effects to the Kusama Shield UI.
Settings
| Property | Range | Default | Description |
|---|---|---|---|
rainMode | boolean | false | Enable/disable rain effect |
particleCount | 10-200 | 100 | Number of particles on screen |
particleSize | 5-60px | 20 | Particle diameter in pixels |
fallingSpeed | 1-10 | 5 | Animation speed level |
Usage
// Enable rain mode
setRainMode(true);
// Set particle count to 50
setParticleCount(50);
Features
- Image Upload: Custom particle images (cropped to circular shape)
- Default Image:
toolbox.pngif no upload - Animation Types:
fall(top→bottom) orfloat(gentle up/down) - Live Preview: Shows animation in settings modal
Technical Details
- Particles use
position: fixed,z-index: 9999,pointer-events: none - CSS animations for GPU acceleration
- Uses
vhunits for full viewport coverage
Performance
- Maximum 200 particles to prevent performance issues
- Uses CSS animations (GPU accelerated)
pointer-events: noneensures no interaction interference
Integrate Kusama Shield
Do you have a feature or integration request?
Open an issue here:
Do you have a token on Kusama Assethub that you want to show in the main UI?
This will be fixed in a soon to-come release, but for now, open an issue like above.
Do you want us to deploy Kusama Shield on another network?
Open an issue here:
Do you need something custom?
Email kusamashield at segfault dot net
Using @kusamashield/shielded-transfers on Paseo AssetHub
This is for paseo testnet, you can also utilize the Kusama Assethub and Polkadot Assethub from this library
Library link:
https://www.npmjs.com/package/@kusamashield/shielded-transfers
A step-by-step guide to depositing and withdrawing shielded PAS tokens.
Prerequisites
- Node.js 18+
- A Paseo AssetHub account with PAS balance (get from faucet)
- Circuit artifacts (included in the npm package)
1. Install
npm install @kusamashield/shielded-transfers ethers
# Or pin a specific version:
npm install @kusamashield/shielded-transfers@0.1.2 ethers
2. Copy Circuit Artifacts
The WASM and proving key files need to be served. For a Node.js script, copy them to your project:
cp node_modules/@kusamashield/shielded-transfers/dist/withdraw_phase2_fixed.wasm ./
cp node_modules/@kusamashield/shielded-transfers/dist/withdraw_phase2_fixed_0001.zkey ./
For browser apps, these go in
public/so the library can fetch them viafetch().
3. Connect
import { ethers } from "ethers";
import { PASEO_CONFIG } from "@kusamashield/shielded-transfers";
const provider = new ethers.JsonRpcProvider(PASEO_CONFIG.rpcUrl);
const wallet = new ethers.Wallet("0xYOUR_PRIVATE_KEY", provider);
4. Deposit PAS
import { shieldedPaseo } from "@kusamashield/shielded-transfers";
const deposit = await shieldedPaseo(
ethers.ZeroAddress, // token address (ZeroAddress = native PAS)
"10", // amount in human-readable format
wallet, // ethers signer
PASEO_CONFIG // chain config (optional, defaults to Paseo)
);
console.log("TX:", deposit.hash);
console.log("Secret:", deposit.secret); // save this for withdrawal
console.log("Nullifier:", deposit.nullifier); // save this for withdrawal
What happens:
- Generates random
secretandnullifier - Computes
commitment = poseidon2([poseidon2([amount, 0]), poseidon2([nullifier, secret])]) - Computes
nullifierHash = poseidon1([nullifier]) - Calls
depositNative(commitment, nullifierHash)on the shield contract, sendingamountPAS - Contract stores
deposits[nullifierHash] = {amount, asset, isSpent: false}and inserts commitment into the Merkle tree
5. Wait for Confirmation
// Wait ~2 blocks for the deposit to be confirmed
await new Promise(r => setTimeout(r, 10000));
6. Withdraw PAS
import { withdrawPaseo } from "@kusamashield/shielded-transfers";
const result = await withdrawPaseo(
ethers.ZeroAddress, // token address
"10", // amount to withdraw
wallet.address, // recipient address
deposit.secret, // from step 4
deposit.nullifier, // from step 4
0, // leaf index (0 for local single-leaf tree)
wallet,
PASEO_CONFIG
);
console.log("TX:", result.hash);
What happens internally:
- Computes the same commitment from
(amount, asset, nullifier, secret) - Builds a local single-leaf LeanIMT with just that commitment
- Generates new random
secretandnullifierfor any change commitment - Calls
snarkjs.groth16.fullProve()with the v4 withdraw circuit - Formats the proof for Solidity and calls
withdrawNative()on the shield contract - Contract verifies the Groth16 proof, checks
deposits[nullifierHash]is unspent and has sufficient funds, transfers PAS to recipient
Complete Example
import { ethers } from "ethers";
import {
PASEO_CONFIG,
shieldedPaseo,
withdrawPaseo,
} from "@kusamashield/shielded-transfers";
async function main() {
const provider = new ethers.JsonRpcProvider(PASEO_CONFIG.rpcUrl);
const wallet = new ethers.Wallet("0xYOUR_PRIVATE_KEY", provider);
console.log("Balance:", ethers.formatEther(await provider.getBalance(wallet.address)), "PAS");
// Deposit
const deposit = await shieldedPaseo(ethers.ZeroAddress, "10", wallet);
console.log("Deposit TX:", deposit.hash);
// Wait
await new Promise(r => setTimeout(r, 10000));
// Withdraw
const result = await withdrawPaseo(
ethers.ZeroAddress, "10", wallet.address,
deposit.secret, deposit.nullifier, 0, wallet
);
console.log("Withdraw TX:", result.hash);
}
main().catch(console.error);
Pallet Assets (e.g. USDC, PSILV)
For non-native tokens, use the asset variants:
import {
shieldAssetPaseo,
withdrawAssetPaseo,
getPalletAssetPrecompile,
} from "@kusamashield/shielded-transfers";
// Deposit 50 PSILV (asset ID 50000867)
const deposit = await shieldAssetPaseo(50000867, "50", wallet);
// Wait
await new Promise(r => setTimeout(r, 10000));
// Withdraw
const result = await withdrawAssetPaseo(
50000867, "50", wallet.address,
deposit.secret, deposit.nullifier, 0, wallet
);
How It Works (Why No On-Chain Tree Sync?)
The Merkle root in the withdrawal circuit is a private input — it is never checked on-chain.
| Component | Checked On-Chain? | Purpose |
|---|---|---|
nullifierHash | ✅ Yes | Prevents double-spending |
| Groth16 proof | ✅ Yes | Proves knowledge of valid (nullifier, secret, value) |
This is why we build a local single-leaf tree — the root matches the proof, but doesn't need to match the on-chain tree. Security comes entirely from nullifierHash verification.
Gas Estimates
| Operation | Gas | Notes |
|---|---|---|
| Deposit (native) | ~80k | Simple storage write |
| Withdraw (native) | ~300k | Groth16 verification + transfer |
| Deposit (pallet asset) | ~120k | Includes ERC20 approval + transfer |
| Withdraw (pallet asset) | ~350k | Asset transfer from contract |
Troubleshooting
siblings array must have exactly 128 elements— EnsuretreeDepth: 128in config and the circuit matchesWithdraw(128).deposit[nullifierHash] not found— The nullifier from step 4 doesn't match what's on-chain. Ensure you used the same secret/nullifier pair.deposit already spent— The nullifier has already been used in a prior withdrawal. Each deposit can only be withdrawn once.insufficient balance— Fund your account via the Paseo faucet.- Proof generation takes ~17s — Normal for Groth16 with the
Withdraw(128)circuit on a single thread. Browser with SharedArrayBuffer is faster (~5-10s).
Available Functions
| Function | Purpose |
|---|---|
shieldedPaseo(asset, amount, signer, config?) | Deposit native PAS |
shieldedPolkadot(asset, amount, signer, config?) | Deposit native DOT |
shieldedKusama(asset, amount, signer, config?) | Deposit native KSM |
withdrawPaseo(asset, amount, recipient, secret, nullifier, leafIndex, signer, config?) | Withdraw native PAS |
withdrawPolkadot(asset, amount, recipient, secret, nullifier, leafIndex, signer, config?) | Withdraw native DOT |
withdrawKusama(asset, amount, recipient, secret, nullifier, leafIndex, signer, config?) | Withdraw native KSM |
shieldAssetPaseo(assetId, amount, signer, config?) | Deposit pallet asset on Paseo |
shieldAssetPolkadot(assetId, amount, signer, config?) | Deposit pallet asset on Polkadot |
shieldAssetKusama(assetId, amount, signer, config?) | Deposit pallet asset on Kusama |
withdrawAssetPaseo(assetId, amount, recipient, secret, nullifier, leafIndex, signer, config?) | Withdraw pallet asset on Paseo |
withdrawAssetPolkadot(assetId, amount, recipient, secret, nullifier, leafIndex, signer, config?) | Withdraw pallet asset on Polkadot |
withdrawAssetKusama(assetId, amount, recipient, secret, nullifier, leafIndex, signer, config?) | Withdraw pallet asset on Kusama |
Reference
- Library: codeberg.org/KusamaShield/shielded-transfers
- npm:
@kusamashield/shielded-transfers - Paseo RPC:
https://kusama-rpc.laissez-faire.trade/ - Shield contract:
0x3099889C1538f0200B831181cbfb532a4e9A418F - Paseo faucet: faucet.polkadot.io
Library API
Native Token Functions
| Function | Purpose |
|---|---|
shieldedPaseo(asset, amount, signer, config?) | Deposit native PAS |
shieldedPolkadot(asset, amount, signer, config?) | Deposit native DOT |
shieldedKusama(asset, amount, signer, config?) | Deposit native KSM |
withdrawPaseo(asset, amount, recipient, secret, nullifier, leafIndex, signer, config?) | Withdraw native PAS |
withdrawPolkadot(...) | Withdraw native DOT |
withdrawKusama(...) | Withdraw native KSM |
Pallet Asset Functions
| Function | Purpose |
|---|---|
shieldAssetPaseo(assetId, amount, signer, config?) | Deposit pallet asset on Paseo |
shieldAssetPolkadot(assetId, amount, signer, config?) | Deposit on Polkadot |
shieldAssetKusama(assetId, amount, signer, config?) | Deposit on Kusama |
withdrawAssetPaseo(assetId, amount, recipient, secret, nullifier, leafIndex, signer, config?) | Withdraw pallet asset on Paseo |
Utility Functions
| Function | Purpose |
|---|---|
buildChainMerkleTree(chainName, customConfig?) | Rebuild tree from on-chain events |
getChainMerkleProof(chainName, leafIndex, customConfig?) | Get proof for deposit |
formatChainAmount(wei, chainName) | Format to human-readable |
parseChainAmount(amount, chainName) | Parse from human-readable |
Chain Configurations
// Paseo AssetHub (v4)
PASEO_CONFIG: ChainConfig {
contract: 0x3099889C1538f0200B831181cbfb532a4e9A418F,
treeDepth: 128,
rpcUrl: "https://kusama-rpc.laissez-faire.trade/"
}
// Polkadot AssetHub
POLKADOT_CONFIG: ChainConfig {
contract: 0xe55B85441Bc39532f279Cf24059f02DFbcf87051,
treeDepth: 128,
rpcUrl: "https://eth-rpc.polkadot.io/"
}
// Kusama AssetHub
KUSAMA_CONFIG: ChainConfig {
contract: 0xDC80565357D63eCa67F3f020b6DD1CE1fD0E1Ed8,
treeDepth: 254,
rpcUrl: "https://eth-rpc-kusama.polkadot.io/"
}
V5 Proxy Withdrawals
Overview
V5 introduces proxy-based withdrawal patterns for enhanced privacy and gas efficiency.
Key Concepts
Proxy Pattern
- Users deposit into a proxy contract first
- Proxy handles Merkle tree updates and proof generation
- Reduces on-chain footprint of withdrawal operations
- Enables batching multiple withdrawals in single transaction
Contract Addresses (Paseo AssetHub)
| Contract | Address | Purpose |
|---|---|---|
| Shield | 0x327773DAF3E145623b9CF5E78c8Cbc09c657e14b | Main shield contract |
| Verifier | 0x471Aea61fA91cb122f1A00Da5f476eB69dc114Ed | ZK proof verification |
| LeanIMT128 | 0xFF8Ead5c88CdEf89f9E5514F00e1D9db09ac5Ca5 | Merkle tree storage |
| PoseidonT3 | 0x1d165f6fE5A30422E0E2140e91C8A9B800380637 | Hash function |
Withdrawal Flow
- Build Merkle Tree: Reconstruct from contract events starting from
deploymentBlock: 9592061 - Generate Proof: Use
withdraw_phase2_fixedcircuit with 7 public signals - Validate Root: Compare local
tree.rootwithcontract.currentRoot() - Execute Withdrawal: Call
withdrawNative()orwithdraw()with proof
7 Public Signals
V5 contract requires uint[7] calldata pubSignals:
pubSignals = [root, nullifierHash, existingValue, newValue,
existingSecret, newSecret, assetId]
Use padTo7Signals: true when calling zkWithdraw() for native tokens (assetId = 0).
Event Signatures
Deposit(address,bytes32,uint256) // token, commitment, amount
Withdrawal(address,uint256,address,uint256) // caller, amount, recipient, nullifierHash
NewCommitment(bytes32) // commitment
Known Limitations
- Proxy contract
0x94196fF8Fb407F84414dfd6749d88D3FBc1dd1F6has 85 leaves without historical events - Use main contract for full tree reconstruction
- Addresses must be lowercase to avoid EIP-55 checksum validation errors
Troubleshooting
- Duplicate commitments: Track with
Set<string>to prevent double insertion - Wrong tree depth: Local tree must match contract's expected
treeDepth: 128 - Event scanning slow: Use
deploymentBlockto skip historical blocks
V5 Partial Withdrawals (UTXO Chain)
Overview
V5 supports partial withdrawals using UTXO-style value splitting. Users can withdraw portions of their shielded balance while maintaining privacy.
Partial Withdrawal Flow
Deposit
Create commitment with full value:
const deposit = await shieldedPaseo(ZeroAddress, "100", wallet);
// commitment encodes: poseidon2([poseidon2([amount, 0]), poseidon2([nullifier, secret])])
Partial Withdrawal
Withdraw only portion, remainder goes to change commitment:
const result = await withdrawPaseo(
ZeroAddress, // token (native)
"30", // withdraw amount (partial)
wallet.address, // recipient
deposit.secret, // original secret
deposit.nullifier, // original nullifier
leafIndex, // position in tree
wallet
);
// Change: 70 tokens → new commitment with fresh nullifier/secret
UTXO Model
- Each deposit creates a UTXO (unspent transaction output)
- Withdrawal consumes one UTXO and may create one change UTXO
- Change UTXO uses new random
nullifierandsecret - Both nullifiers are marked as spent in contract
Circuit Requirements
- Use
withdraw_phase2_fixedcircuit - Build single-leaf local LeanIMT for proof generation
- Merkle root is private input (not verified on-chain)
- Requires 128-element
siblingsarray
Tree Reconstruction
// Start from deployment block for efficiency
const tree = await buildMerkleTreeFromContract(
provider,
contractAddress,
abi,
false,
rpcUrl,
deploymentBlock: 9592061
);
// Prevent duplicate commitments from withdrawal events
const insertedCommitments = new Set<string>();
if (!insertedCommitments.has(commitmentStr)) {
tree.insert(commitment);
insertedCommitments.add(commitmentStr);
}
Root Validation
const contractRoot = await contract.currentRoot();
if (tree.root !== contractRoot) {
throw new Error("Tree mismatch - refresh required");
}
Gas Considerations
| Operation | Gas | Notes |
|---|---|---|
| Full withdrawal | ~300k | No change commitment |
| Partial withdrawal | ~350k | Creates change UTXO |
Security Notes
- Save
(secret, nullifier)pair immediately after deposit - Never reuse nullifier — each can only be spent once
- Change commitments are indistinguishable from original deposits
Kusama Shield Comparison to Tracked Protocols
Comparison of Kusama Shield against other privacy protocols in the ecosystem.
| Property | Kusama Shield | Privacy Pools | Railgun | Hinkal | Curvy | Fluidkey |
|---|---|---|---|---|---|---|
| Confidentiality | Yes | No | Yes | Yes | Partial | No |
| Anonymity | Yes | Linkability | Yes | Yes | Partial | Linkability |
| Asset Privacy | Yes | No | Partial | Partial | Partial | No |
| Plausible Deniability | No | No | No | No | No | Yes |
| Censorship Resistance | Yes(strong) | Yes (ragequit) | Yes | No | No | Yes |
| Compliance Gates | None | ASP (withdraw) | POI (app) | Chainalysis | Predicate | None |
| Client-side Proving | Yes | Yes | Yes | Optional/TEE | No | N/A |
| Partial Withdrawals | Yes | Yes | Yes | Yes | Yes | N/A |
| Implementation Maturity | 2: Testnet + Mainnet <1 year | 4: Mainnet 1+ yr | 5: Mainnet 2+ yr | 3: Mainnet <1 yr | 3: Mainnet <1 yr | 4: Mainnet 1+ yr |
Key Differentiators
Kusama Shield Advantages
- No compliance gates — fully permissionless withdrawals
- Strong censorship resistance — no centralized control points
- Full asset privacy — all shielded assets maintain confidentiality
- True anonymity set — unlinkable deposits/withdrawals
Implementation Notes
- Uses Groth16 ZK proofs (snarkjs)
- Merkle root is public input (must match on-chain tree) — unlike v4 where root is private
- Supports native tokens and pallet assets (ERC20-like)
- 128-depth LeanIMT tree (256 leaves max before upgrade)
Performance Benchmarks (PolkVM)
Powered by 30x customized Poseidon on PolkVM (Rust → PVM):
| Operation | Paseo Gas | Ethereum Gas | Improvement |
|---|---|---|---|
| Single Poseidon hash | 2,706 | 32,800 | 12x cheaper |
| Depth-20 Merkle path | 37,956 | 605,000 | 16x cheaper |
| Groth16 verification | 3,990 | 202,216 | 51x cheaper |
| Shielded pool deposit | ~45K ($0.19) | ~$54 | 270x cheaper |
| Shielded pool withdrawal | ~7K ($0.03) | ~$15 | ~500x cheaper |
Max Poseidon hashes per block: 39 (Solidity: 1, exceeds limit) Architecture: Solidity logic + Rust Poseidon + Groth16 verification
Reference
Protocol data and maturity ratings sourced from https://private-transfers.pse.dev/.
Offramp (USDC to Fiat)
Overview
Convert shielded USDC to fiat currency through the ZKP2P peer-to-peer protocol.
Architecture
- Source: Polkadot network (user sends DOT)
- Bridge: DOT → ETH (gas) and DOT → USDC (for offramp)
- Destination: Base network (for USDC offramp execution)
Flow
Step 1: Bridge DOT → ETH (for gas)
- Users send DOT to a deposit address
- Receive ETH on Base network for transaction fees
- Required if Base ETH balance < $1.5 equivalent
Step 2: Bridge DOT → USDC
- Users send DOT to receive USDC on Base
- Can use existing USDC balance on Base (skips this step)
- Rate estimation via
/exchange_rateendpoint
Step 3: Offramp USDC → Fiat
- Approve USDC spending on Base
- Create deposit with platform/payment details
- Order sent to ZKP2P orderbook for P2P fulfillment
Platforms
| Platform | Currencies |
|---|---|
| Cash App | USD |
| Chime | USD |
| Mercado Pago | ARS, BRL, MXN |
| Monzo | EUR, GBP |
| N26 | EUR |
| PayPal | Multiple fiat pairs |
| Revolut | EUR, GBP, USD |
| Venmo | USD |
| Wise | Multiple fiat pairs |
| Zelle | USD |
Supported Fiat Currencies
- ARS (Argentine Peso)
- AUD (Australian Dollar)
- CHF (Swiss Franc)
- EUR (Euro)
- GBP (British Pound)
- MXN (Mexican Peso)
- SGD (Singapore Dollar)
- THB (Thai Baht)
- USD (US Dollar)
Supported Assets
The offramp supports all pallet-assets on Polkadot and Kusama via the ERC20 precompile system.
Asset Precompile Addresses
Pallet assets use the precompile address format: 0x{assetIdHex}00000000000000000000000001200000
Common assets:
- USDC: Asset ID 1 (via precompile on Asset Hub)
- USDT: Asset ID varies by chain
- PSILV: Asset ID 50000867 on Paseo AssetHub
Asset Shielding
Use the @kusamashield/shielded-transfers library to shield assets before offramping:
// Shield PSILV on Paseo
const deposit = await shieldAssetPaseo(50000867, "100", wallet);
// Bridge to Base and offramp
// See integrate_sdk.md for withdrawal flow
Key Addresses
- USDC (Base):
0x833589fCD6eDb6E08f4c7C32D4f71b54bdA02913 - Offramp Contract:
0x777777779d229cdF3110e9de47943791c26300Ef - Base Chain ID: 8453
Troubleshooting
- Insufficient gas: Bridge DOT → ETH first
- Approval failure: Ensure USDC allowance for offramp contract
- Order expired: Complete within 10 minutes
- Network mismatch: Auto-switches to Base if needed
Video Demo
Watch the full video demo showing the complete offramp flow from DOT bridging to fiat withdrawal.
Deploy Kusama Shield Interface
Requirements:
Clone:
git clone https://codeberg.org/KusamaShield/Interface && cd Interface/
Build wasm:
cargo install wasm-pack
wasm-pack build --target web
rm -rf public/pkg/
cp -r pkg/ public/
Install node packages:
npm install -f
Run locally:

npm run local
Use
npm run devto run it on all public network interfaces
Run a public instance
You should run a public instance! We encourage everyone to do so.
git clone https://codeberg.org/KusamaShield/Interface
cd Interface/ && npm install -f
npm run build
Run:
npm run local
Put Kusama Shield behind a firewall
You are adviced to put the react interface behind a firewall such as:
- nginx + https://github.com/owasp-modsecurity/ModSecurity
- Coraza
Nginx setup example:
Modify vite.config.ts:
import react from '@vitejs/plugin-react'
import { defineConfig } from 'vite'
import path from 'path'
//import { NodeGlobalsPolyfillPlugin } from '@esbuild-plugins/node-globals-polyfill';
// https://vitejs.dev/config/
export default defineConfig({
plugins: [react()],
build: {
target: 'esnext',
},
worker: {
format: 'es',
},
// Cross-Origin-Isolation headers enable SharedArrayBuffer, which lets
// snarkjs/ffjavascript use multi-threaded WASM for multiexponentiation.
// Without these, groth16.prove() runs single-threaded (~40s → ~5-10s).
server: {
port: 6666, // Vite listens here (no root needed)
hmr: {
protocol: 'wss',
host: 'changethistoyourwebsite.com',
// REMOVE THIS: port: 443,
clientPort: 443, // Browser connects here through nginx
},
allowedHosts: ['changethistoyourwebsite.com'],
headers: {
'Cross-Origin-Opener-Policy': 'same-origin',
'Cross-Origin-Embedder-Policy': 'require-corp',
},
},
preview: {
headers: {
'Cross-Origin-Opener-Policy': 'same-origin',
'Cross-Origin-Embedder-Policy': 'require-corp',
},
},
assetsInclude: ['**/*.wasm'],
optimizeDeps: {
include: ['dayjs', 'dayjs/plugin/relativeTime', 'dayjs/locale/en'],
},
})
Add it to nginx:
#cat /etc/nginx/sites-available/mywebsite
server {
# listen 80;
server_name mywebsite;
location / {
proxy_pass http://localhost:6666;
# Or serve static files: root /path/to/your/static/files;
# Add other directives as needed.
proxy_http_version 1.1;
# WebSocket support
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection "upgrade";
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
}
listen 443 ssl; # managed by Certbot
ssl_certificate /etc/letsencrypt/live/mywebsite/fullchain.pem; # managed by Certbot
ssl_certificate_key /etc/letsencrypt/live/mywebsite/privkey.pem; # managed by Certbot
include /etc/letsencrypt/options-ssl-nginx.conf; # managed by Certbot
ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem; # managed by Certbot
}
server {
if ($host = mywebsite) {
return 301 https://$host$request_uri;
} # managed by Certbot
listen 80;
server_name mywebsite;
return 404; # managed by Certbot
access_log /var/log/nginx/xapiaccess.log;
}
Replace mywebsite with my domain and grab a free tls(https) certificate with certbot:
https://certbot.eff.org/instructions
Run with IPFS:
Note: Most ipfs gateways block wasm via the http headers which is a problem for all WASM sites being served over IPFS.
Build project:
npm run build
ipfs add -r dist/
IPFS links:
https://ipfs.github.io/public-gateway-checker/
Run with Docker or Podman
A public docker image of the interface is avaliable here:
https://hub.docker.com/r/kusamashield/interface
Run with podman:
Podman is a great alternative to docker that does not require root to run.
Using one command you can run the Kusama Shield interface locally.
podman run -p 5173:5173 docker.io/kusamashield/interface:v0.1
now open your browser and visit: http://localhost:5173
Run with docker:
Pull image:
docker pull kusamashield/interface:v0.1
Run:
docker run -p 5173:5173 kusamashield/interface:v0.1
References:
https://podman.io/
https://hub.docker.com/
Operator guide
Host Kusama Shield UI instances
Best pratice:
- Own your own hardware
- Always respond to abuse requests with a link to the terms of service, ideally within 24hours
- Keep your systems up to date and happy.
- use ssh public key authentication
- Put Kusama Shield react app behind a proxy
- Always keep a good social relationship with your ISP.
Use your own hardware:
Buying a used server on ebay and asking your local data center or a datacenter nearby for a one unit rack slot, is a great and cost effective way to actually own your own hardware and have more control. Colocation costs are different depending on where(you can also ship your server somewhere cheaper) but for a single unit server your looking at 30-80Euro's a month for the European market. The most price effective way to is often to ask local datacenters or maybe you nknow someone working for a company that has server racks?.
Host using a VPS:
Select a VPS provider, ideally one from Tor's recommended providers | Good Bad ISPs.
Operator Guide - Terms of Service
By hosting an instance and/or using Kusama Shield you agree to the following Terms of Service:
Terms of Service
1. Acceptance of Terms
By accessing and using Kusama Shield, you agree to be bound by these Terms of Service and all applicable laws and regulations.
2. Service Description
Kusama Shield provides a privacy-focused Zero Knowledge token shielding User Interface that allows users to shield and unshield tokens on supported decentralized networks.
3. User Responsibilities
- You are responsible for maintaining the security of your wallet and secret keys
- You must ensure you have sufficient funds for transactions
- Developers and Operators of this website are not liable for any type of Regulatory actions or legal consequences arising from the use of the Platform
- You are responsible for verifying transaction details before confirming
4. Risk Disclosure
- Kusama Shield comes with no warranty
- Cryptocurrency transactions are irreversible
- Kusama Shield is early stage open source software and may contain bugs
- You acknowledge the risks associated with blockchain technology
- The service is provided "as is" without warranties
5. Privacy
- We do not store your private keys or transaction secrets
- This platform does not guarantee anonymity
- All transactions are processed by decentralized blockchain networks without any middlemen
- We do not process transactions or hold any private keys
- The Pool utilizes zero-knowledge proofs to verify transactions and asset holdings without revealing underlying data
- As a host of this website, I do not select the material transmitted through this website that I run, and I have no practical means of either identifying the source of such material or preventing its transmission
- No userdata is ever stored at the host of the Kusama Shield UI
6. Prohibited Use
Users must not:
- Use the Platform for illegal activities (e.g., money laundering, terrorism financing)
- Exploit vulnerabilities, disrupt hosting or engage in attacks against the Platform
- Misrepresent affiliation with the Platform's developers or operators
- Violate applicable laws in their jurisdiction
7. Limitation of Liability
We are not liable for any losses, including but not limited to:
- Lost or stolen secret keys
- Network issues or blockchain congestion
- Incorrect transaction parameters
Developers and maintainers are not financial advisors or custodians of user funds.
Acceptance of Terms
By using the Platform, you confirm that you:
- Understand the risks of decentralized networks and privacy tools
- Assume full responsibility for your interactions with the Platform
- Release all maintainers, operators, and developers from liability
Disclaimer: This document is not legal advice. Consult a qualified attorney for compliance matters.
XCM Transfers
Send token transfers to and from other chains using XCM.
Kusama Shield is deployed on Paseo Hub chain
Supported Chains:
- Paseo Relay
- Paseo Assethub
- Paseo Hub
- Paseo Hydration
- Paseo Pop
Bridge:

1: Connect wallet
Connect your browser wallet and select a substrate/polkadot address.
2: Select to and from chain
Make sure you have funds on your account, use the faucet if needed:
faucet.polkadot.io
3: Press bridge
Tested xcm asset sending routes:
Paseo Relay:
- Relay > Assethub
- Relay > Paseo hub
-
Relay > Paseo Hydration
Unstable route, do not use -
Relay > Paseo Pop
Unstable XCM channel
Paseo Assethub:
- Assethub > Relay
-
Assethub > Paseo hub
No XCM channel open right now. See more here - Assethub > Hydration
-
Assethub > Paseo Pop
Polkadot.js Apps Chain link
Paseo Hub:
- Hub > Relay
- Hub > Assethub No supported channel.
-
Hub > Hydration
No open supported XCM channel. -
Hub > Paseo Pop
No open supported XCM channel. Polkadot.js App Chain link
Kusama Shield Roadmap 2026
Feature list for 2026
Privacy features to enhance and support the next generation of shielded Pools.
Q1
- Extended UI + testing
Testing suit for the interface - Balance checks and block explorer support
- Metamask and wallet connect support
Support for the major EVM browser wallet - Privacy Dashboard with k-anonymity scores
Answering the question: How private is my transaction? - Proxy withdrawals
Ability to withdraw tokens from the shielded pool via a new address
Q2
- Smart contract user simulator on Paseo
- Zero Knowledge logic moved from Solidity into Polkavm
LeanIMT and more rust RISC-V optimized features.
Polkavm programs extended scope - Massive user documentation and examples
Documentation for 40+ different L1 assets, how they can utilize Kusama Shield. - Audit
Audit of smart contracts contracts, write up and audit report publishing by ZK expert.
Implementation of extended features and patches of bugs + readjustment of some of the zk logic(especially the merkle tree)
Kohaku integration
We want to integrate Kusama Shield directly into Kohaku, making it easy for future applications to integrate. We aim to make Kusama Shield the best Kohaku integration and submit an integration or once past audit https://github.com/ethereum/kohaku
Why is Kohaku important?
Kohaku aims to cater to dapp developers, making it easy to provide shielded transfers, we want to t Most solidity dapp developers
Q3 - Going stable
Support for a lot of Assets by default,
Bring your own assets(ability to just paste in an kusama ah asset address),
ipfs UI fork ui button(deploy a new version of the UI by the click of a button)
Ability for smart contract to withdraw asset directly to parachains via xcm precompiles
Do you have features you want to see in Kusama Shield?
Open a codeberg issue here: https://codeberg.org/KusamaShield/Interface/issues.
Extra features that will be added:
- ISMP integration

- Non custodial(kyc) offramps
Non custodial Offramps in the main UI - Yielding Shielded Pools
Earn rewards for shielding your tokens
Contribute to Kusama Shield
No matter if you are technical or not, you can help us spread awareness of Kusama Shield and Privacy!
For relatively fast support, email: kusamashield@segfault.net
Can I contribute to Kusama Shield Anonymously?
Yes! We are using codeberg for exactly this reason. Anyone can use the tor browser, sign up fast and contribute to Kusama Shield at codeberg.org/kusamashield.
Host an instance
If you have experience hosting or/and as a system administrator, we encourage you to host a public instance of Kusama Shield. Let us know and we will share it and link it here on the wiki.
Dealing with Abuse complaints
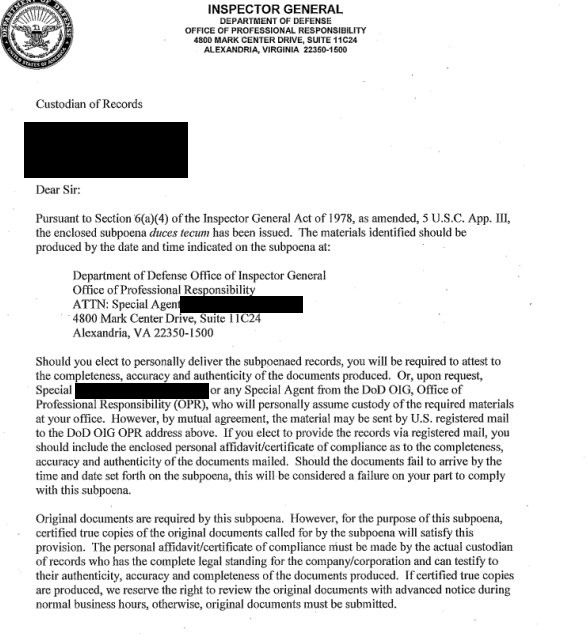 Pattern trolls, legal staff and automated systems may, like any other website, send you takedown and/or abuse requests. If you recieve an email like the above, you are adviced to reply(IDEALLY NOT FROM YOUR PERSON ACCOUNT BUT FROM A GENERIC ONE, so its better pratice to reply from a legal@mydomain rather than nameofperson@domain) with a link to the Terms of Service. Which can be found at the end of all pages in the Kusama Shield UI.
As a hosting provider you do not handle custody over any assets and all you are hosting is a way to interact with a decentralized system, do not let pattern trolls scare you into taking the site down.
Pattern trolls, legal staff and automated systems may, like any other website, send you takedown and/or abuse requests. If you recieve an email like the above, you are adviced to reply(IDEALLY NOT FROM YOUR PERSON ACCOUNT BUT FROM A GENERIC ONE, so its better pratice to reply from a legal@mydomain rather than nameofperson@domain) with a link to the Terms of Service. Which can be found at the end of all pages in the Kusama Shield UI.
As a hosting provider you do not handle custody over any assets and all you are hosting is a way to interact with a decentralized system, do not let pattern trolls scare you into taking the site down.
Host as a tor hidden service:
Spinning up a .onion address for your instance is a fast way to add an extra layer of privacy.
Note:
This torrc file will change depending on your operating system.
when running the application as a tor hidden service, its important that you bind only the local interface, so when starting the app run npm run local not npm run dev
/etc/tor/torrc
We will tell tor to listen on port 80 and forward all requests to our local instance:
HiddenServiceDir /var/lib/tor/shield/
HiddenServicePort 80 127.0.0.1:5173
Restart tor and you will find the domain in the /var/lib/tor/shield/hostname file:
cat /var/lib/tor/other_hidden_service/hostname
aj4giwh2mu2n77f2ji22pqp7lbk2qmz2uhcafnz5oefnwbwfb22zniyd.onion
Grab the domain and try it either with adding .to and pasting it in your browser or by using torsocks and curl:
torsocks curl -v aj4giwh2mu2n77f2ji22pqp7lbk2qmz2uhcafnz5oefnwbwfb22zniyd.onion
Can you connect? if everything is good you can share your .onion publicly!
If you are renting a VPS and only want to host a tor instance, we recommend that you scan your VPS IP with nmap to make sure nothing extra is running on any port:
nmap -sC -sV -p- SERVERIPGOESHERE
If you see a strange port open, on linux you can login and check which process is listening:
lsof -i | grep THEPORTNUMBERGOESHERE
Help out with documentation
Fix spelling mistakes, improve our documentation. Help more people understand Kusama Shield by translating documentation.
testing the software and reporting bugs
Spread the word about Kusama Shield
Talk about Kusama Shield, spread the word, advocate for privacy
Guerilla Marketing
Promote Kusama Shield by:
- Writing articles/blog posts
- Showing demo's
- Spreading the word
- Creating designs/images/videos/meme's
Print Kusama Shield merch

Previous we have printed out holographic stickers, this is fun and low cost option to spread awareness of Privacy and Kusama Shield.
You can find the designs for the stickers here:
codeberg.org/KusamaShield/Graphics
Kusama Privacy
Kusama Network is pushing towards being the home for resilient privacy applications. By utilizing Zero Knowledge and Kusama Assethub smart contract platform, we can build true resilient apps.

Kusama Governance:
Projects can utilize funding from Kusama's treasury by the power of opengov.
kusama.polkassembly.io
kusama.subsquare.io
Good papers on privacy:
Ring signatures/How to Leak a Secret
Zerocoin: Anonymous Distributed E-Cash from Bitcoin
Zexe: Decentralized Private Computation
Useful Zero Knowledge links:
Halo2 Hero course
0xparc
Zero Knowledge with Anna Rose podcast
zk-kit from PSE
Poseidon hashing in PolkaVM
Circom ZK toolkit
Noir ZK DSL
Get started with building on kusama today:
- Kusama.network
- Zero Knowledge groth16 program on Kusama Assethub example
- polkavm rust program example
Privacy projects on Kusama:
- Shield.markets
- Todo add more
Public Kusama Privacy Chat
Join the public kusama privacy chat group and productively contribute to brining more privacy to kusama:
https://matrix.to/#/#privacyinthebirdnest:matrix.org
